
Bible Prophecy, Signs of the Times and Gog and Magog Updates with Articles in the News
Archaeologist: The lost ark is beneath Jerusalem and new technology can find it without moving a stone
or millennia, the Ark of the Covenant has been the most sought-after relic in human history. Now, a biblical archaeologist from Tennessee believes the answer to its whereabouts may lie not in a distant land, but directly beneath the ancient stones of Jerusalem, and he has the technology to prove it.
Dr. Chris McKinney, associate professor of biblical archaeology at Lipscomb University, has put forward a serious academic hypothesis: the Ark may be concealed in subterranean voids beneath the City of David, the archaeological site immediately south of the Temple Mount where the Jewish Temples once stood. McKinney has even identified a cutting-edge instrument to test his theory: a muon detector.
Muon detectors track subatomic particles produced when cosmic rays collide with Earth’s atmosphere. These particles penetrate deep into the ground, allowing scientists to map hidden structures and voids without disturbing a single stone. Early scans of the City of David have already revealed previously unknown subterranean openings beneath the site. And critically, because the Ark is described in the Bible as overlaid entirely with gold — inside and out — it would register unmistakably on such a scan.
McKinney has anchored his search in three ancient traditions about the Ark’s fate following the Babylonian destruction of Jerusalem in 586 BCE. Each places the prophet Jeremiah at the center of a desperate effort to conceal the Ark before the city fell. The first tradition, which McKinney calls the Mount Legend, holds that priests hid the Ark and other sacred objects in underground chambers or tunnels beneath the Temple Mount itself — the very ground upon which the Dome of the Rock now stands. This theory has driven centuries of speculation and is constrained by the fact that archaeological excavation beneath the Temple Mount remains largely forbidden due to its extraordinary religious and political significance. As McKinney described it, the area is “one of archaeology’s biggest blind spots” since traditional work with “the spade or the trowel” is not possible there due to Palestinian aggression.
The second tradition, the Rock Legend, describes Jeremiah hiding the Ark at a mysterious rocky location between two mountains near Jerusalem, though the precise site remains debated among scholars. The third and oldest account, drawn from the Book of 2 Maccabees places Jeremiah carrying the Ark to a cave on Mount Nebo, the mountain where Moses died. McKinney notes that despite their geographic differences, all three accounts share a consistent thread: the Ark was deliberately hidden, not destroyed or captured.
The Bible itself offers a striking parallel to this urgency. When King Josiah ordered the Levites to return the Ark to the Temple, he told them: “Put the holy ark in the house which Solomon the son of David, King of Israel, built; it shall not be a burden upon your shoulders” (2 Chronicles 35:3). The Ark’s keepers understood that their charge was not merely ceremonial — it was existential. The Aron was the physical throne of the Shekhinah, the divine presence. Allowing it to fall into Babylonian hands was simply not an option.
McKinney’s documentary, Legends of the Lost Ark, released on April 7, 2026, brings his research to a wider audience. He explores not just the three major traditions but also the technological frontier that may finally allow researchers to peer into spaces that have been sealed for 2,600 years. Beyond muon detectors, he points to ground-penetrating radar, seismic scanning, and electrical resistivity tomography as tools that could, in theory, map tunnels and chambers beneath the Temple Mount without a single unauthorized dig.
He is careful to frame this as a long-term possibility, not an imminent excavation. Religious sensitivities, political realities, and logistical barriers remain formidable. But McKinney told reporters he is “excited and hopeful for what will come from that.”
The Sages have long taught that the Ark was among the items hidden away before the destruction of the First Temple, preserved for a future redemption. The Talmud Yerushalmi and other rabbinic sources hold that Josiah himself hid the Ark in a subterranean chamber, anticipating the coming catastrophe. If McKinney’s technology eventually reaches beneath the Temple Mount and the scans return something extraordinary — a rectangular gold-plated object in a sealed chamber — it would be the archaeological find of the century, but, more importantly, it would be a moment the Jewish people have been waiting for since Nebuchadnezzar’s armies appeared on the horizon.
Logged And Tracked: How License Plate Readers Could Map Your Entire Life
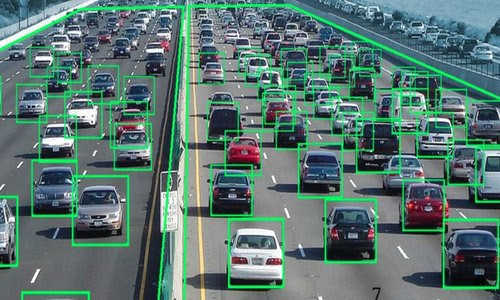
What began as a tool to catch criminals is quietly becoming something far more powerful-and far more dangerous. Across the United States, more than 80,000 automated license plate reader (ALPR) cameras-many deployed by Flock Safety–are scanning, recording, and storing the movements of millions of vehicles every single day.
These systems promise safety. But increasingly, they are revealing something else: how easily surveillance infrastructure can be turned inward on the very people it was meant to protect.
A recent report highlighted a disturbing reality–law enforcement officers have used these systems not just for investigations, but to track romantic partners, exes, and even strangers. At least 14 documented cases uncovered by the Institute for Justice show officers allegedly abusing access to track individuals for personal reasons. In nearly every case, consequences followed. But the deeper issue remains: if individuals with limited authority can misuse such tools, what happens when institutions decide to use them systematically?
This is where the conversation shifts from misconduct… to potential.
Because ALPR systems don’t just capture license plates–they capture patterns, routines, and lives.
1. The Quiet Mapping of Faith and Belief
Consider a simple Sunday morning.
Dozens–sometimes hundreds–of vehicles pull into church parking lots across America. Cameras positioned on nearby roads or intersections log each plate. They log when cars arrive. When they leave. How often they return.
Now imagine that data compiled over weeks, months, years.
It would not take sophisticated artificial intelligence to build a database of regular churchgoers. Patterns would emerge almost instantly: who attends weekly, who comes occasionally, who stopped coming altogether. Cross-reference that with other data–home addresses, workplaces–and suddenly, you don’t just have a list of cars. You have a map of religious life.
Today, that may sound hypothetical. But the underlying capability already exists.
And history offers a sobering reminder: governments have not always treated religious populations with neutrality. In less stable times, such data could be used to monitor, pressure, or even target communities of faith. What begins as passive observation can become active scrutiny.
2. Tracking Dissent Before It Begins
License plate readers don’t just see individuals–they see gatherings.
Protests, political rallies, community meetings–all of them generate traffic patterns that are easily captured. A few cameras placed strategically can log nearly every vehicle attending an event. Over time, that data can identify repeat participants.
This raises a critical question: what happens when dissent becomes trackable?
A government–local, state, or federal–could theoretically compile lists of individuals who attend certain protests or political events. Not based on suspicion of wrongdoing, but simply based on presence. With enough data, it becomes possible to identify organizers, frequent attendees, and networks of association.
Even if never acted upon, the mere existence of such a capability can have a chilling effect. People may begin to ask themselves: Is attending this event worth being tracked?
Freedom doesn’t always disappear with force. Sometimes it erodes quietly, through awareness that someone is watching.
3. Building a Comprehensive Movement Profile
Perhaps the most far-reaching potential lies in aggregation.
Individually, a single scan of a license plate reveals very little. But when thousands of scans are compiled, a detailed portrait of a person’s life begins to form. Where they work. Where they shop. Who they visit. What routes they take. When they travel. How often they leave home.
This is not speculation–it is the natural outcome of large-scale data collection.
Now imagine that database combined with other systems: toll records, facial recognition, mobile location data, digital payment history. The result is something unprecedented–a near-complete behavioral map of ordinary citizens.
Such a system doesn’t require warrants in the traditional sense if access controls remain loose. As critics have pointed out, in many cases, officers can query databases with minimal justification–sometimes little more than typing a reason into a field.
That is not robust oversight. That is trust-based access to powerful tools.
And trust, history shows, is not always enough.
The Illusion of “We Can Have It All”
Supporters of ALPR systems, including leadership at Flock Safety, often argue that safety and civil liberties can coexist–that technology can deliver both security and freedom.
It’s an appealing idea.
But it assumes perfect restraint in an imperfect world.
The recent misuse cases exposed by the Institute for Justice are not just isolated incidents–they are warning signs. They show that when vast amounts of personal movement data are made easily accessible, misuse is not just possible–it is inevitable.
And if misuse occurs at the individual level, it raises a more pressing concern: what happens when misuse becomes policy?
A Line That Once Crossed Is Rarely Redrawn
Surveillance systems rarely shrink. They expand. They integrate. They become normalized.
The danger is not just what these tools can do today–but what they make possible tomorrow.
Because once a society accepts that every movement can be logged, stored, and analyzed, it has already crossed a line that is difficult to reverse.
The question is no longer whether the technology works.
It’s whether we fully understand what we are building–and who might one day control it.
Pressure Points – Converging Events Will Soon Force Next Steps With Iran

Tehran authorities are increasing internal security measures, deploying elite units, restricting communication channels and using advanced monitoring to suppress potential protests. They are also relying more on external militias and vulnerable populations to bolster enforcement capacity.
Economic vulnerability, especially tied to oil production and sanctions, poses a major risk to sustaining control. A convergence of leadership uncertainty, economic strain and infrastructure disruption could undermine the regime’s ability to maintain authority.
Recently, the Iranian Supreme National Security Council convened an emergency meeting. The issues on the agenda were the most urgent: operational readiness and internal suppression. They discussed several topics, first and foremost:
In recent days, there have been reports of a massive deployment of Sarallah units, the elite Revolutionary Guard forces responsible for securing Tehran, at central squares and strategic intersections.
There is no internet. The public has shifted to using SMS. However, the regime is operating advanced monitoring systems to detect keywords in text messages to arrest protest organizers before they take to the streets.
One of the clearest signs of the regime’s concern about losing loyalty among local policing forces is its growing reliance on external actors. Reports from recent days indicate the arrival of “advisers” and special units from Hashd al-Shaabi/Popular Mobilization Forces (the Shi’ite militias from Iraq) to the provinces of Khuzestan and Sistan-Baluchistan, as well as to Tehran and Mashhad.
The Fatemiyoun Division: The regime continues to recruit stateless Afghan refugees. There are approximately half a million refugees within Iran’s borders, lured by promises of dollar salaries and Iranian identification documents, to serve as cannon fodder on the front lines of confrontations with protesters.
The regime is operating under a geographically based risk management approach. In core cities such as Tehran, Mashhad and Isfahan, the emphasis is on visible presence (show of force) to deter the middle class.
In Kurdish areas such as Mahabad, Ilam and Sanandaj, and in Balochi regions, repression is far more lethal. There, the regime employs light artillery and surveillance drones, out of concern that armed resistance groups may exploit the civil unrest for military activity.
Centralized regimes
The elimination of Ali Khamenei undoubtedly marks the beginning of the regime’s collapse. Historically, centralized regimes rely on a cult of personality and a hierarchy in which all decisions converge on a single individual. When that figure disappears suddenly, an internal succession struggle begins, weakening the regime’s ability to suppress.
A historical example is the Soviet Union after Joseph Stalin’s death in 1953. Although the regime did not collapse immediately, the death of the centralized dictator led to internal power struggles, including the elimination of Lavrentiy Beria, head of the secret police, and initiated the process of “de-Stalinization” that undermined the foundations of the Communist Party over time.
In the Iranian case, such a vacuum would prevent the Basij and the Revolutionary Guards from receiving clear orders at a critical moment.
Closing the Strait of Hormuz turns against Iran. Within a few weeks of an American blockade, there would be a technical collapse of resources. The issue of water infiltration into oil wells is critical. In the oil industry, once drilling stops and reservoir pressure changes, the damage can be irreversible or extremely costly to repair.
A historical example is Venezuela from 2019 to the present. The combination of heavy American sanctions and mismanagement of the national oil company led to a situation in which Venezuela, despite having the largest oil reserves in the world, could not produce oil for sale. The result was a total collapse of the electricity grid, hyperinflation and shortages of basic food that drove millions to flee. In Iran, oil is not just money. It is the channel through which the regime pays its security apparatus.
When a state loses $500 million a day, it loses the ability to subsidize essential goods such as bread, fuel and electricity. History shows that as long as the public is hungry but the regime remains well-resourced and unified, it can survive. But when the economy collapses to the point where the ordinary soldier cannot feed his family, loyalty breaks.
A historical example is the French Revolution of 1789. France’s deep economic crisis, combined with droughts that led to bread shortages, drove the masses into the streets. The royal army, composed of people whose families were also suffering from hunger, eventually refused to fire on the protesters. This is the moment when a regime begins to fail, when its coercive power no longer obeys it.
If the elements are brought together, they form a potentially destabilizing equation—leadership vacuum, infrastructure collapse and extreme economic pressure leading to loss of control over the streets.
So why is the regime still confident? The Iranian leadership is relying on a “resistance economy” and smuggling networks through Iraq, Afghanistan and China. They believe that as long as the “core of control” retains weapons and food, they will be able to suppress any uprising, even at a high human cost.
The key lies in Washington. If the Americans allow flexibility in sanctions, the regime may sustain itself. If the pressure is airtight, oil assets could become liabilities, and time would work against the regime at an accelerating pace.
We are at a moment of mounting pressure, with signs of instability already visible. Yet timing is shaped by external considerations. The World Cup, beginning on June 11, creates a global preference for stability over disruption. At the same time, the U.S. political calendar is moving toward November’s midterm elections, with campaign dynamics intensifying from the summer.
History suggests that when American leadership is caught between strategic objectives and electoral pressures, compromise often follows. For policymakers in Washington, developments in Tehran may be weighed less as decisive geopolitical turning points and more as variables within a broader political calculus. The tension between long-term strategy and short-term stability remains unresolved.